Background
- In recent months, Blackpoint has observed an uptick in ISO file malware. These virtual disks contain malicious executables and have the capability to automatically execute when double-clicked.
- ISO files are not historically a file type scanned by conventional antivirus (AV) solutions.
- The files are being padded to exceed the upload limit of AV solutions, as a means of bypassing them.
- Adversaries are becoming more advanced in their methods of bypassing AV by using publicly available third-party and native operating system tools to gain remote access.
Findings
- Blackpoint uncovered an ISO file containing malware which was downloaded onto a customer’s computer and executed without interference from AV.
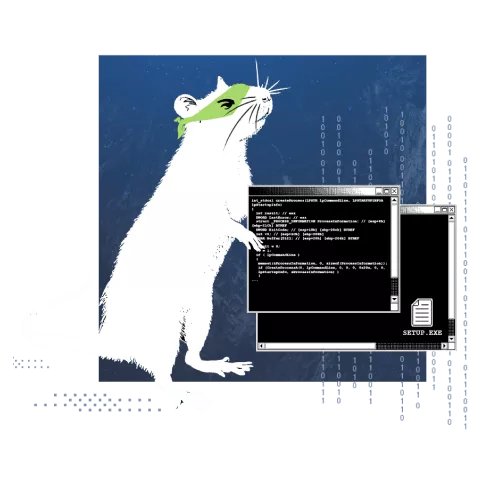
- The malware used a free tool named AutoIT3 to carry out its malign actions on the system, including the installation of a known remote access tool named Arechclient2.
- The destructive payload is split into the AutoIT3 executable and a script. The script file is not scanned by AV.
- The techniques and the remote access tool were heavily obfuscated to hide functionality from the untrained eye.
Recommendations
- In today’s threat landscape, having the capability to detect and respond to advanced hacker tradecraft is crucial.
- Your business should ensure there is a security solution in place that has visibility into file formats and behaviors that are outside the scope of AV.
To learn more about the Adversary Pursuit Group’s findings regarding the usage of Arechclient2, read our latest whitepaper, Ratting Out Arechclient2. There, we dive into execution, obfuscation, indicators of compromise (IoCs), and more.
Monitoring for Tradecraft
Adversaries are continuing to advance their techniques via the usage of public, free, native, or whitelisted tools. With Blackpoint Cyber, these malicious tactics will be stopped by security professionals, even when they surpass your automated defenses. Furthermore, APG exists to research and reverse engineer attacks so that our partners have the necessary intel to strengthen their defenses.
Stay Ahead of the Quickest Threats
- Trust our experts to investigate incidents and halt threats around the clock.
- Defeat threat actors with network visualization, endpoint security, and cloud security.
- Focus on your business while we fully manage your security efforts.
- Strengthen your defenses with threat intel from the Adversary Pursuit Group.